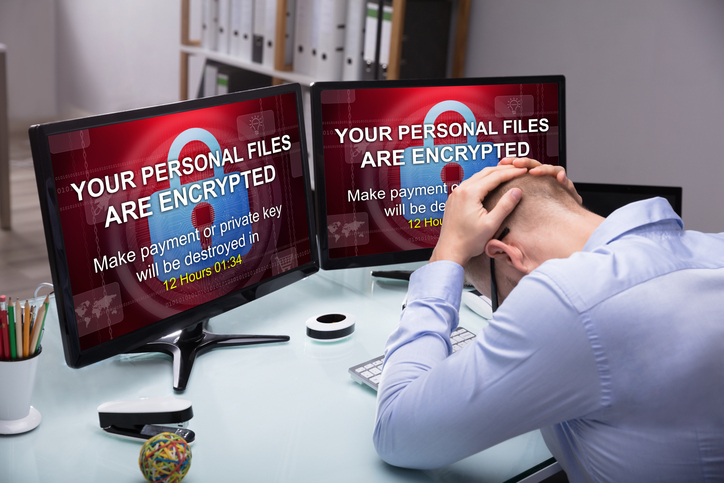
Cybercriminals lock victims out of computer and network files – sometimes destroying data – and extort cash to get that data back. That’s a ransomware attack, costing businesses billions worldwide.
Ransomware can spread by the simplest of user actions. Email phishing, or Business Email Compromise (BEC) – fraudulent and deceptive emails posing as legitimate messages – is perhaps the most common propagation method. Social media clickbait, particularly using fake accounts masquerading as friends or colleagues, is common also. Simply visiting an infected website can corrupt your system, even if the user doesn’t click anything on the web page.
How common is ransomware? There’s bad news and good news. The bad news: attacks are extremely common, with thousands of organizations being probed every day. The good news: savvy IT professionals are fending off attacks, so infections are still comparatively rare. However, attacks are on the rise and cybercriminals are growing more sophisticated.
Ransomware attacks are hitting businesses of all sizes, from a few employees to enterprise corporations. Individuals get infected also, especially those without good antivirus protection. Government agencies and health care organizations have become prime targets.
Data Loss and Financial Risk
Ransomware encrypts computer files and network drives, then demands a ransom in exchange for a decryption key. Most victims end up paying the ransom. Ransomware can be difficult, if not impossible, to crack, and paying the ransom can be the only way to get data back.
Costs of recovery can be enormous. The ransom itself can run from thousands to hundreds of thousands of dollars, even approaching $1 million dollars. The real cost of recovery runs easily into the millions. FedEx reported losses of more than $300 million before operations were fully restored. The total cost to US business is estimated at $75 billion or more per year, with downtime costing around $8,500 per hour.
Cybercriminals typically demand payment in Bitcoin. Cryptocurrency affords substantial anonymity, making it nearly impossible to track perpetrators. Even if they could be identified, cybercriminals often work over international borders. Jurisdiction issues makes prosecution almost impossible.
Preventing Ransomware
Ransomware protection is a complex endeavor involving technology, education and best practices. You need the right tools – the right information – and the right business processes.
Key steps to protect your data include:
- Maintain up-to-date antivirus/malware protection, especially on email. Do your research for best programs, including buyer reviews on popular online retail sites.
- Perform regular external backups, and quarantine them from your network as soon as they’re completed. Keep archival history as much as possible.
- Train employees. Malware is most often spread by human behavior, e.g. clicking an email phishing link or social media clickbait. Proper training can minimize risk by educating staff about the risk of suspicious links.
- Maintain strong firewall protection to minimize the risk of a single infected machine spreading malware into your network.
- Keep all enterprise software updated with the latest releases and patches. Software firms are constantly improving security, and outdated software is riskier.
- Administer IT user permission security so employees have access only to the software and functionality required for their job roles.
- Disable macro scripts on files shared via email – an important component of training.
Along with preventative measures, create a contingency plan. If you are hit with ransomware, you’ll be better prepared to cope if you have plans in place to continue operations and speed up recovery.
Setting up a cryptocurrency wallet should be part of the contingency plan. If your business is hit – and you decide to pay the ransom – you’ll be able to pay much sooner if you already have this in place.
See these resources for more detail on what you can do to protect your business.
What to Do If Infected
More than half of targets don’t report ransomware attacks, according to FBI estimates. This is likely driven by concerns over bad publicity. Financial and business process recovery is bad enough without adding in a PR nightmare.
However, it’s critical to notify the FBI if your systems are infected. The FBI is the lead federal agency for cybercrime. Their investigative and technology capabilities are state-of-the-art, and no one is better equipped to help you understand your options and recover your data.
The FBI suggests that you do not pay the ransom. The decision is up to your company leadership, and it’s true that most victims do pay. In many cases, the cost of paying the ransom is far less than the potential losses from operational downtime.
Ransomware removal often involves wiping systems clean and restoring uninfected files from backups. It’s a delicate business best left to a professional cybersecurity company.
It Can Happen to Your Business
Ransomware and cybercrime are on the rise. Costs to businesses are going up.
Education and preparation are the best defenses against cybercrime. Responsible management needs to be proactive. Threats are real, cybercriminals are serious, and today’s IT professionals are armed with the tools and the knowledge to keep their companies safe.
